I was poking around in a Swann NVR to see whether I could customise it to suit my needs a bit better.
The NVR was easy enough to pull apart with only 5 screws on the outside holding the case on.
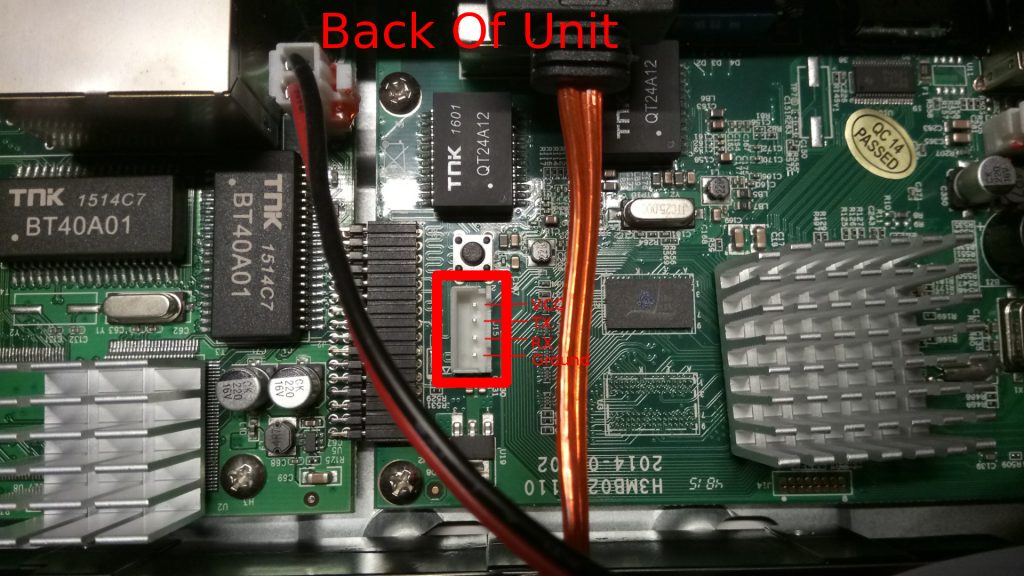
After taking the case off, I identified the J15 header as the serial port.
Serial port header is J15
The settings I used for the serial port is as follows:
Baud: 115200
8 Data bits
No Parity
1 Stop Bit
115200-8-N-1 in common notation
Plugging in my trusty USB to TTL adapter and I found that I had instant root.
I had a poke around and found out that it runs linux –
# uname -a
Linux (none) 3.4.35_hi3535 #6 SMP Wed Jun 24 11:30:14 CST 2015 armv7l GNU/Linux
Since it runs linux, I extracted the /etc/shadow file and cracked the root password, even though it’s not much use to me at the moment.
root:$1$mWYiIVv8$/taigZpC9w/xvglK1TwNV/:0:0::/root:/bin/sh ## password is 20120515
This runs busybox 1.16, and has a few partitions on flash –
# mount
rootfs on / type rootfs (rw)
/dev/root on / type cramfs (ro,relatime)
proc on /proc type proc (rw,relatime)
sysfs on /sys type sysfs (rw,relatime)
tmpfs on /dev type tmpfs (rw,relatime)
usbfs on /proc/bus/usb type usbfs (rw,relatime)
devpts on /dev/pts type devpts (rw,relatime,mode=600)
/dev/mtdblock5 on /mnt/app type cramfs (ro,relatime)
/dev/mtdblock6 on /mnt/para type yaffs2 (rw,relatime)
tmpfs on /var type tmpfs (rw,relatime)
tmpfs on /mnt/tmp type tmpfs (rw,relatime,size=2048k)
tmpfs on /mnt/cache type tmpfs (rw,noatime,nodiratime,size=8192k,nr_inodes=4000)
This NVR uses a ARMv7 CPU –
# cat /proc/cpuinfo
Processor : ARMv7 Processor rev 1 (v7l)
processor : 0
BogoMIPS : 1987.37
processor : 1
BogoMIPS : 1993.93
Features : swp half thumb fastmult edsp tls
CPU implementer : 0x41
CPU architecture: 7
CPU variant : 0x4
CPU part : 0xc09
CPU revision : 1
Hardware : hi3535
Revision : 0000
Serial : 0000000000000000
The hi3535 seems to be a 1GHz ARM Cortex A9 CPU.
I did a Netstat to see what was listening
# netstat -l
Active Internet connections (only servers)
Proto Recv-Q Send-Q Local Address Foreign Address State
tcp 0 0 0.0.0.0:9000 0.0.0.0:* LISTEN
tcp 0 0 0.0.0.0:85 0.0.0.0:* LISTEN
netstat: /proc/net/tcp6: No such file or directory
udp 0 0 0.0.0.0:3000 0.0.0.0:*
udp 0 0 0.0.0.0:3000 0.0.0.0:*
udp 0 0 0.0.0.0:59836 0.0.0.0:*
udp 0 0 0.0.0.0:2000 0.0.0.0:*
udp 0 0 0.0.0.0:59093 0.0.0.0:*
udp 0 0 0.0.0.0:45807 0.0.0.0:*
udp 0 0 0.0.0.0:32761 0.0.0.0:*
The NVR also uses uboot
U-Boot 2010.06 (Dec 02 2014 - 14:50:19)
So hopefully I can use uBoot to do some modifications to the partitions. The kernel command line shows where the root partition is, and also which partition is how big.
Kernel command line: mem=140M console=ttyAMA0,115200 root=/dev/mtdblock4 rootfstype=cramfs mtdparts=hinand:512K(uboot1),1920K(uboot2),128K(bootargs),4352K(kernel),12288K(fs),32768K(app),8192K(para),2048K(logo),11264K(ipc_img),128M@0(wholeflash),1024K@73472K(uid_img)
The partition laylout looks like this –
Creating 11 MTD partitions on "hinand":
0x000000000000-0x000000080000 : "uboot1"
0x000000080000-0x000000260000 : "uboot2"
0x000000260000-0x000000280000 : "bootargs"
0x000000280000-0x0000006c0000 : "kernel"
0x0000006c0000-0x0000012c0000 : "fs"
0x0000012c0000-0x0000032c0000 : "app"
0x0000032c0000-0x000003ac0000 : "para"
0x000003ac0000-0x000003cc0000 : "logo"
0x000003cc0000-0x0000047c0000 : "ipc_img"
0x000000000000-0x000008000000 : "wholeflash"
0x0000047c0000-0x0000048c0000 : "uid_img"
So when I have time, I should be able to dump the partitions to a TFTP server, modify them as I need, then re-upload them to make the modifications I need…hopefully.

I was wondering if you got any further with this?
Not yet, haven’t had the time unfortunately.
Were you interested in anything in particular?
HI SirLagZ.
It is very interesting article you have. I have got the same unit. I did firmware update two days ago and the unit not working any more. No support from Swann and they said that my warranty is void as I did update myself.
I opened NVR and noticed jtag port too as serial. At work we were messing with IAR boards and using JTAG to program it. I looked in firmware and found that the first section is Uboot and then the code.
1. I just Wondering if it would be possible to flash the unit with this official firmware using Jtag or using serial?
2. What utility i need to use if go with serial?
3. Do i need to erase all section in prom or only some regions?
I need to do it any way or I have to buy new unit which is costly and don’t like to give up.
All findings with images and steps I will provide to you, so you get more traffic to your site and help other people who was left on their own.
Thank you
Hi Alex,
If you did the firmware update via the software on the Swann NVR itself, then that should never ever void the warranty, otherwise how would consumers fix security flaws in Swann hardware?
I would go back to Swann and tell them to get their act together and provide you with a solution.
But back onto your questions –
I’m sure it is possible to flash it via JTAG, however I’m not too familiar with JTAG myself so I can’t be of much help there, sorry! 🙁
I don’t think you’d be able to do it via Serial, as we don’t have write access to the flash chip.
You might be able to do it with a hardware flasher similar to these –
https://www.ebay.com.au/itm/USB-Programmer-CH341A-Burner-Chip-24-EEPROM-BIOS-Writer-25-SPI-Flash-WIN7-TE839/332469748754
And grab a clip to save you from having to desolder the flash chip –
https://www.ebay.com.au/itm/For-SOIC8-SOP8-Flash-Chip-IC-Test-Clip-with-SPI-Cable-Programmer-BIOS-TL866A-CS/202178755085
Maybe? That’s an option?
Hi Alex,
Just found this page the last 4 months I been searching for ways to reboot or restore my nvr7400 I also did the firmware upgrade and it stopped working correctly also, and of course Swann didn’t want to know about it pretty much. I was wondering if you got anywhere with your system did you manage to get it operating correctly again if so any tips thanks in advance ??
Hey guys how are use? I was wondering if any of use worked this out I had the same thing happen to my nvr when I did firmware upgrade and have been trying to find a way to repair it for months now ?
Swann also didn’t want to know about it and that was that.
Cheers Mick
Well add me to another one who locked up a 7400 NVR by doing an update. Did anyone have any luck with restoring one?? I was told it may be possible to access the unit by its IP address. So far with my limited knowledge, it does not look like my NVR is able to transmit its IP address to the router. (if that is the correct term.)
I got a Reolink one that I think is identical, if you reboot it from UART and then hold down space or something you’ll stop it at the bootloader and that will let you reflash it (at least thats what help said, I didn’t actually try it yet)
How did you determine that this was a serial port and not something else?
Educated guess
HI
Wow you lads obviously know what you are doing.
I have the same NVR 7400 8 camera CCTV system its only 22 months old and has stopped working.
I’ve spoken to Swann customer support who informed me its out of warranty.
The problem l’ve got is there’s no lights working front or back it will not power up.
The items l’ve checked is the switching adapter 240v input 48v output. I put my ear to adapter is has slight buzzing and no clicking when connected to NVR .
The support team seemed to think it was possibly the surveillance Hand drive at fault and advised me to disconnect and the see if it would power. Up.
I disconnected the hard drive and it still will not power up?
The only thing l could see was a build up of fluff around fan possibly restricting air flow.
I don’t know what parts could be effected by heat.
I would appreciate any help.
John
This password of 20120515 seems to be common on Swann DVRs. It is also the root password on the DVR8-4550 (and likely anything else which identifies its hardware as H2MB14). There is an open telnet port, user “root” with password “20120515” gets you in, no problems.
For the DVR8-4550, it is possible to hook into the boot process before the DVR software starts, by inserting a USB stick with a file named “autoexec.sh” in the root directory. I have used this to get rid of the default root password and to have the system start an NTP server to keep the time constantly up to date (something the DVR8-4550 will not do despite what the documentation says. My USB stick contains the following files:
autoexec.sh
#!/bin/sh
mount -t tmpfs tmpfs /tmp
cd /mnt/usb
[ -d /tmp/autoexecs ] || mkdir /tmp/autoexecs
cp autoexecs/* /tmp/autoexecs
cd /tmp/autoexecs
chmod 755 *.sh
./custom-inits.sh &
autoexecs/ntp-server:
pool.ntp.org
autoexecs/passwd
root:*:0:0::/root:/bin/sh
autoexecs/custom-inits.sh
#!/bin/sh
mount -o bind passwd /etc/passwd
sleep 30
/usr/sbin/ntpd -p `cat ntp-server`
Doing anything more than this is left as an exercise to the reader.
This is very interesting. I might have to try this out when I get the chance to, giving myself root SSH or telnet access would be handy
Is there anyplace to get a new mother board H3MB02_V110..
Mine just stopped working, getting power from supply and is at 48V as listed on power supply.. Not sure where or what to do now..
Thanks
Vicky
Would be nice to be able to have 8tb or larger drives i think the max is 6tb
With root access to the NVR, you could see if there’s a workaround for the size limit. I haven’t actually tried any large HDDs in my NVR so don’t know what the limit is.